Table of Contents
ToggleThe numbers tell a sobering story about mobile app security in 2025. According to Digital.ai‘s 2025 Application Security Threat Report, 83% of applications are under constant attack—a dramatic increase from 65% in 2024. This represents nearly a 20% surge in attack rates across all industries, with telecom (91%), financial services (87.5%), automotive (86%), and healthcare (78.5%) being the most targeted sectors.
The disconnect between perception and reality is alarming. While many developers believe their apps are secure, research shows that over 75% of applications contain at least one security vulnerability, and unpatched vulnerabilities are involved in 60% of data breaches.
The financial stakes have never been higher. IBM’s 2024 Cost of a Data Breach Report reveals that the average cost of a data breach reached an all-time high of $4.88 million in 2024—a 10% increase from the previous year. Beyond immediate costs, the reputational damage is severe, with studies indicating that a significant portion of customers would abandon an app after experiencing a security breach.
Why Mobile App Security Practices Are Critical in 2025?
The answer is simple: cyber threats are evolving faster than traditional defenses. Modern mobile apps face sophisticated AI-powered attacks, supply chain vulnerabilities, and compliance requirements that basic security measures cannot address effectively.
Mobile app security practices have evolved from simple password protection to comprehensive defense systems that include behavioral analytics, real-time threat detection, and automated incident response. These practices are essential for today’s apps that handle sensitive user data, financial transactions, and personal information.
Moreover, implementing robust mobile app security practices provides competitive advantages through enhanced user trust, regulatory compliance, and reduced operational risks. As a result, more organizations are investing in comprehensive security frameworks, driving demand for advanced protection solutions.
Top 15 Mobile App Security Practices To Secure Your App
The following are the 15 essential mobile app security practices that you should implement to secure your application. We have organized these practices into four strategic layers for comprehensive protection.
1. Zero Trust Authentication Implementation
Move beyond traditional login screens to continuous authentication using behavioral biometrics, device fingerprinting, and contextual analysis for verification throughout user sessions. Modern zero trust systems analyze factors like typing patterns, swipe gestures, and location consistency to maintain security without disrupting user experience.
Companies like Microsoft report 99.9% reduction in account compromises after implementing continuous authentication. This approach monitors user behavior continuously, flagging anomalies like unusual login times or unfamiliar devices.
Banking apps particularly benefit from this technology, detecting fraudulent access attempts within seconds while maintaining seamless experiences for legitimate users.
2. End-to-End Encryption with Forward Secrecy
Implement advanced cryptographic protocols that protect data even if encryption keys are compromised, securing both data in transit and at rest with regularly rotated keys. Forward secrecy ensures that past communications remain secure even if current encryption keys are breached, using ephemeral keys that change with each session.
Signal and WhatsApp successfully demonstrate this approach, with over 2 billion users protected by end-to-end encryption with forward secrecy. This technology generates unique session keys that are discarded after use, preventing retroactive decryption of captured data. Healthcare apps handling sensitive patient data particularly benefit from forward secrecy implementation.
3. Secure API Gateway Protection
Deploy comprehensive API security with authentication, rate limiting, input validation, and real-time threat detection to protect backend communications and data exchanges. API gateways serve as critical security checkpoints, filtering malicious requests and preventing common attacks like SQL injection and DDoS attempts.
Organizations using robust API gateways report 85% reduction in successful cyberattacks targeting their mobile applications. These systems implement OAuth 2.0 authentication, request throttling, and payload validation to ensure only legitimate traffic reaches backend systems.
E-commerce platforms particularly benefit from API gateway protection, safeguarding payment processing and customer data from sophisticated attacks.
4. Code Obfuscation and Anti-Tampering
Use advanced code obfuscation techniques and runtime application self-protection (RASP) to prevent reverse engineering, debugging, and unauthorized application modifications. Code obfuscation transforms readable code into functionally equivalent but difficult-to-understand versions, making reverse engineering significantly more challenging.
Financial apps using advanced obfuscation report 70% reduction in successful reverse engineering attempts. RASP technology detects tampering attempts in real-time, automatically shutting down compromised applications before damage occurs.
Gaming companies frequently implement these protections to prevent cheating and intellectual property theft, maintaining competitive advantages and protecting revenue streams from unauthorized modifications.
5. Secure Session Management
Implement automatic session expiration, short-lived tokens, device binding, and proper session invalidation across all user devices and application instances. Effective session management prevents unauthorized access through stolen or compromised session tokens by implementing strict timeout policies and token rotation.
Netflix implements sophisticated session management, automatically detecting and terminating suspicious sessions across multiple devices. Short-lived tokens, typically expiring within 15-30 minutes, reduce attack windows while device binding ensures sessions can’t be transferred between devices.
Healthcare applications particularly benefit from strict session management, ensuring patient data remains protected even if devices are lost or stolen.
6. Behavioral Analytics and Anomaly Detection
Deploy machine learning algorithms that analyze user patterns, device characteristics, and interaction behaviors to identify potential fraud and account takeover attempts in real-time.
These systems establish baseline user behaviors, flagging deviations like unusual transaction amounts, atypical navigation patterns, or suspicious device characteristics. PayPal’s behavioral analytics prevent over $6 billion in potential fraud annually by detecting anomalous user behaviors within milliseconds.
Machine learning models continuously adapt to evolving user patterns while identifying sophisticated attack techniques. Social media platforms leverage behavioral analytics to detect bot accounts and automated abuse, maintaining platform integrity and user trust.
7. Real-Time Threat Detection Systems
Implement AI-powered threat detection that analyzes network traffic, user behavior, and system events to identify and respond to emerging security threats automatically. These systems process millions of data points per second, identifying attack patterns and zero-day exploits faster than human analysts.
Darktrace’s AI threat detection systems identify cyberattacks within seconds, providing 92% accuracy in threat identification. Real-time analysis enables immediate response to sophisticated attacks like advanced persistent threats (APTs) and coordinated bot campaigns.
Financial institutions particularly benefit from real-time threat detection, protecting against fraud attempts and maintaining regulatory compliance through continuous monitoring.
8. Automated Incident Response
Deploy intelligent response systems that automatically isolate threats, revoke compromised sessions, and alert security teams while maintaining service availability for legitimate users.
Automated response systems execute predetermined security protocols within milliseconds, containing threats before they spread or cause significant damage. IBM’s automated incident response reduces average response times from hours to seconds, minimizing potential damage and recovery costs.
These systems can automatically quarantine suspicious users, block malicious IP addresses, and implement additional authentication requirements. Cloud-based applications particularly benefit from automated response, scaling security measures dynamically based on threat levels and maintaining service availability during attacks.
9. Privacy-by-Design Data Handling
Build data minimization into application architecture with purpose limitation controls, granular consent management, and automatic data lifecycle management for regulatory compliance. Privacy-by-design ensures data protection is embedded throughout application development rather than added as an afterthought.
Apple’s App Store requires privacy-by-design implementation, with 94% of developers adopting enhanced privacy practices since policy introduction. This approach includes collecting only necessary data, implementing granular user consent, and automatically deleting data when no longer needed. Healthcare applications particularly benefit from privacy-by-design, ensuring HIPAA compliance while maintaining functionality and user experience through careful data architecture design.
10. Automated Compliance Monitoring
Implement continuous monitoring systems that track adherence to GDPR, CCPA, HIPAA, and other applicable regulations with real-time compliance reporting and violation alerts. Automated compliance monitoring reduces manual oversight requirements while ensuring consistent regulatory adherence across all application components.
Microsoft’s compliance monitoring systems track over 1,400 regulatory requirements automatically, reducing compliance costs by 40% while improving accuracy. These systems generate real-time reports, flag potential violations, and suggest remediation actions.
Financial services applications particularly benefit from automated compliance monitoring, maintaining adherence to complex regulations like PCI-DSS and SOX while reducing administrative overhead and audit preparation time.
11. Comprehensive Audit Trail Management
Maintain immutable logs of all security events, user actions, and system changes with forensic-quality data retention for investigations and regulatory audits. Comprehensive audit trails provide detailed records of all system activities, enabling forensic analysis and regulatory compliance reporting.
Blockchain-based logging systems ensure audit trail integrity, with organizations reporting 95% improvement in audit preparation efficiency. These systems capture user interactions, system changes, and security events with precise timestamps and digital signatures.
Government applications particularly benefit from comprehensive audit trails, meeting strict accountability requirements while providing detailed records for security investigations and compliance audits.
12. DevSecOps Integration and Secure Development
Embed security throughout development workflows with automated security testing, secure coding practices, and continuous vulnerability assessment in CI/CD pipelines. DevSecOps integration ensures security considerations are addressed throughout development rather than as final-stage additions.
Organizations implementing DevSecOps report 50% reduction in security vulnerabilities reaching production environments. Automated security testing includes static analysis, dynamic testing, and dependency vulnerability scanning integrated directly into development workflows.
Technology companies particularly benefit from DevSecOps integration, accelerating secure software delivery while maintaining high security standards through continuous testing and validation throughout development lifecycle.
13. Over-the-Air Security Updates
Enable real-time security patches and threat response updates without requiring manual user intervention, crucial for mitigating zero-day exploits and emerging threats. Over-the-air updates ensure security patches reach devices immediately, reducing exposure windows for critical vulnerabilities.
Tesla’s over-the-air update system delivers security patches to millions of vehicles within hours of threat identification. These systems can update security configurations, patch vulnerabilities, and deploy new threat detection rules automatically.
IoT applications particularly benefit from over-the-air updates, maintaining security across distributed device networks without requiring physical access or user interaction for critical security improvements.
13. Over-the-Air Security Updates
Enable real-time security patches and threat response updates without requiring manual user intervention, crucial for mitigating zero-day exploits and emerging threats. Over-the-air updates ensure security patches reach devices immediately, reducing exposure windows for critical vulnerabilities.
Tesla’s over-the-air update system delivers security patches to millions of vehicles within hours of threat identification. These systems can update security configurations, patch vulnerabilities, and deploy new threat detection rules automatically.
IoT applications particularly benefit from over-the-air updates, maintaining security across distributed device networks without requiring physical access or user interaction for critical security improvements.
14. Regular Penetration Testing and Vulnerability Assessment
Conduct comprehensive security assessments using both automated tools and manual testing to proactively identify vulnerabilities before attackers can exploit them. Regular penetration testing combines automated vulnerability scanning with expert manual testing to identify complex security weaknesses that automated tools might miss.
Organizations conducting quarterly penetration testing report 60% fewer successful cyberattacks compared to those testing annually. Professional penetration testers simulate real-world attack scenarios, testing both technical vulnerabilities and human factors.
Financial institutions particularly benefit from regular penetration testing, meeting regulatory requirements while identifying sophisticated attack vectors that could compromise customer data and financial systems.
15. Continuous Security Monitoring and Threat Intelligence
Implement 24/7 monitoring systems with threat intelligence integration that tracks security metrics, performance indicators, and emerging threats across all application components. Continuous monitoring provides real-time visibility into application security posture, enabling immediate response to emerging threats and performance issues.
Security operations centers (SOCs) utilizing threat intelligence prevent 85% more attacks through proactive threat identification and response. These systems integrate global threat intelligence feeds, correlating local security events with worldwide attack patterns.
Enterprise applications particularly benefit from continuous monitoring, maintaining security visibility across complex distributed systems while enabling rapid response to sophisticated and coordinated cyberattacks.
Benefits of Implementing Mobile App Security Practices
Implementing comprehensive mobile app security practices provides various advantages to organizations. The top benefits are as follows:
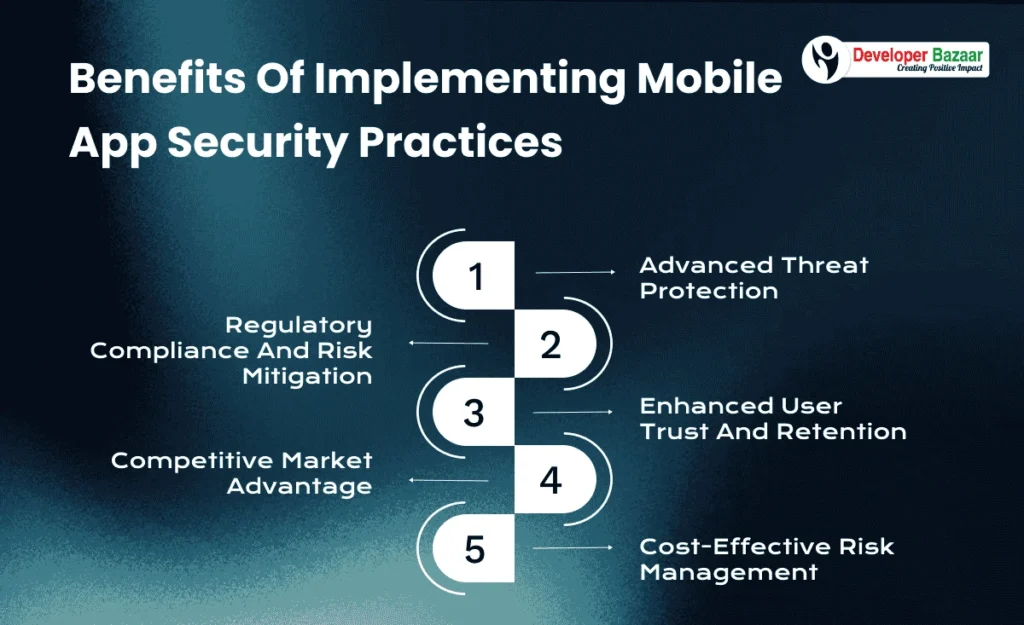
Advanced Threat Protection
Mobile app security practices enable proactive defense against sophisticated cyber attacks including AI-powered threats, social engineering, and zero-day exploits. Advanced security frameworks protect against both known and unknown attack vectors through layered defense mechanisms.
Regulatory Compliance and Risk Mitigation
Comprehensive security practices ensure compliance with GDPR, CCPA, HIPAA, and other data protection regulations. This reduces legal risks and potential fines while building user trust through transparent privacy controls and data handling practices.
Enhanced User Trust and Retention
Research shows that 77% of internet users worldwide worry about personal and sensitive data being stolen, making security a key differentiator in user acquisition and retention. Secure apps demonstrate commitment to user protection and privacy.
Competitive Market Advantage
Organizations with strong security practices gain competitive advantages through reduced breach risks, faster compliance processes, and premium positioning in security-conscious markets. Security excellence becomes a measurable business differentiator.
Cost-Effective Risk Management
Proactive security implementation costs significantly less than breach remediation. With average breach costs exceeding $4.88 million, investing in comprehensive security practices delivers substantial ROI through prevention rather than reaction.
How to Implement Mobile App Security Practices?
Now that you know the benefits, let’s jump into the step-by-step process to implement comprehensive mobile app security practices.
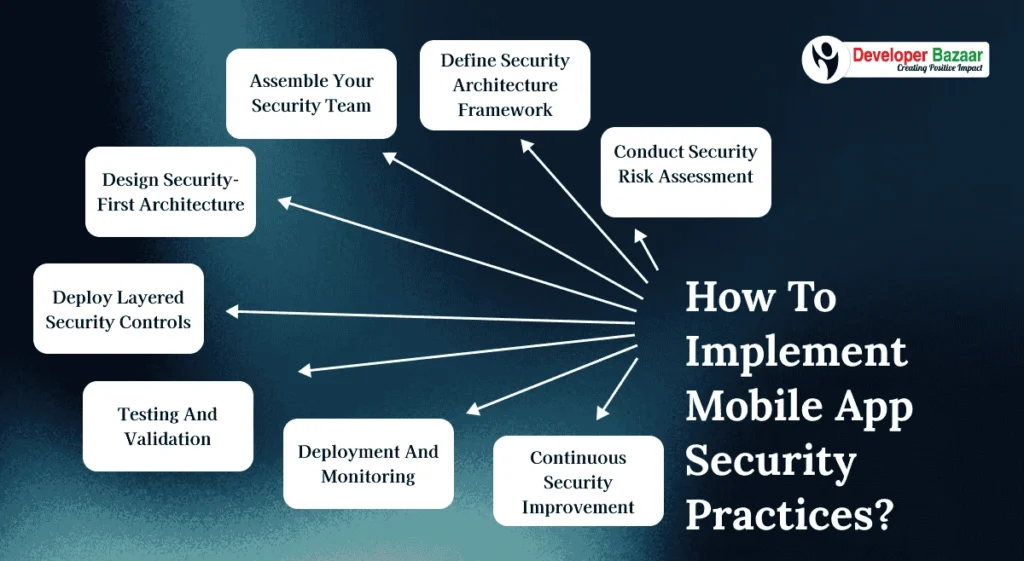
Conduct Security Risk Assessment
Before implementing security practices, conduct thorough security audits to identify existing vulnerabilities and risk exposure across your mobile applications. Analyze current security controls, data flows, and potential attack vectors.
Also, assess your compliance requirements including GDPR, CCPA, and industry-specific regulations. This assessment will help you prioritize security implementations and allocate resources effectively for maximum protection.
Define Security Architecture Framework
After conducting risk assessment, establish your security architecture framework. Decide whether you’ll implement Zero Trust models, defense-in-depth strategies, or hybrid approaches based on your application complexity and threat landscape.
Plan your security implementation phases including foundation layer, intelligence layer, compliance layer, and operations layer. Defining this framework beforehand will streamline your security deployment and ensure comprehensive protection coverage.
Assemble Your Security Team
Implementing mobile app security practices requires specialized expertise in cybersecurity, application security, and compliance management. The complex nature of modern threats demands professionals experienced in AI-driven security, behavioral analytics, and incident response.
We recommend hiring security professionals who have implemented comprehensive security frameworks or partnering with a top mobile app development company that specializes in security-first development approaches.
Design Security-First Architecture
Engage your security architects to design security controls that integrate seamlessly with user experience. Security implementations should be transparent to users while providing robust protection against threats and maintaining application performance.
Focus on security controls that enhance rather than hinder user experience, such as biometric authentication, behavioral analytics, and automated threat response systems that work invisibly in the background.
Deploy Layered Security Controls
Now, implement your security practices across all application layers. Start with foundational security controls including encryption, authentication, and API protection, then add intelligence layers with AI-driven threat detection and behavioral analytics.
Integrate compliance monitoring, audit capabilities, and continuous security monitoring to ensure ongoing protection and regulatory adherence across all application components and user interactions.
Testing and Validation
Once security practices are implemented, conduct comprehensive security testing including penetration testing, vulnerability assessments, and red team exercises. Security validation is crucial for ensuring that implemented controls actually protect against real-world threats.
Conduct ongoing security assessments to verify effectiveness, identify gaps, and validate that security practices remain effective against evolving threat landscapes and attack methodologies.
Deployment and Monitoring
Deploy your secured application with comprehensive monitoring systems that provide real-time visibility into security events, threat indicators, and performance metrics. Ensure monitoring covers all security layers and provides actionable intelligence.
Implement incident response procedures, escalation protocols, and automated response capabilities that can address threats quickly while maintaining service availability for legitimate users.
Continuous Security Improvement
Post-deployment, continuously monitor security effectiveness using metrics like threat detection rates, false positive ratios, and incident response times. Modern security requires ongoing adaptation as threat landscapes evolve.
Regular security updates should include threat intelligence integration, model retraining for AI-driven systems, security patch management, and proactive threat hunting to identify emerging risks before they impact operations.
Cost to Implement Mobile App Security Practices
In this section, you will learn about the costs to implement comprehensive mobile app security practices. The costs depend on multiple factors, such as application complexity, security requirements, compliance needs, technology stack selection, team expertise, and organizational size. To make it easier for you to understand, we have provided a table with implementation cost estimations.
Have a look:
| Implementation Scope | Estimated Investment (in $) |
|---|---|
| Basic Security Framework | $20,000 to $40,000 |
| Comprehensive Security Suite | $35,000 to $60,000 |
| Enterprise Security Platform | $60,000 to $80,000 |
Please note that these are only estimations. Actual costs may vary based on security complexity, compliance requirements, integration needs, and ongoing operational expenses.
Conclusion
This is your complete guide to implementing the 15 best mobile app security practices in 2025. With attack rates reaching 83% of applications and average breach costs exceeding $4.88 million, comprehensive security is no longer optional but essential for business survival and growth.
Implementing mobile app security practices provides numerous benefits, including advanced threat protection, regulatory compliance, enhanced user trust, competitive market advantage, and cost-effective risk management that delivers measurable ROI through prevention rather than remediation.
The evolving threat landscape demands proactive security approaches that combine foundational controls, AI-driven intelligence, compliance frameworks, and continuous monitoring. Organizations that invest in comprehensive security practices now will be better positioned to defend against future threats while capturing market opportunities.
Follow this guide to secure your mobile applications today. If you want professional assistance, reach out to Developer Bazaar Technologies, the leading mobile app development company in Dubai specializing in security-first development and comprehensive protection frameworks.
We have implemented advanced security solutions for numerous organizations across various industries, helping them achieve security excellence while maintaining user experience and operational efficiency. You can explore our security portfolio for detailed case studies and success stories.
FAQs
Q1. What are mobile app security practices?
Mobile app security practices are comprehensive frameworks and techniques designed to protect mobile applications from cyber threats, data breaches, and security vulnerabilities through layered defense mechanisms, compliance controls, and continuous monitoring systems.
Q2. How much does it cost to implement mobile app security practices?
Basic security framework implementation costs $20,000-$40,000, while comprehensive security suites range from $35,000 to $60,000. Enterprise security platforms require $60,000-$80,000+, depending on complexity and requirements.
Q3. How long does it take to implement comprehensive security practices?
Implementation typically takes 2-4 months for basic frameworks, 4-8 months for comprehensive suites, and 8-12 months for enterprise platforms with full integration and testing phases.
Q4. What makes mobile app security practices effective in 2025?
Effectiveness comes from layered defense approaches combining AI-driven threat detection, behavioral analytics, Zero Trust authentication, automated incident response, and continuous monitoring that adapts to evolving threat landscapes.
Q5. What ROI can I expect from mobile app security investments?
Organizations typically see positive ROI within 8-15 months through avoided breach costs, reduced compliance expenses, improved user retention, and operational efficiency gains from automated security systems.
Q6. Which security practices are most critical for mobile apps?
Critical practices include Zero Trust authentication, end-to-end encryption, behavioral analytics, real-time threat detection, secure API protection, and continuous security monitoring integrated throughout application architecture.
Q7. How do I ensure security practices don't impact user experience?
Modern security practices enhance user experience through biometric authentication, invisible behavioral analytics, automated threat response, and seamless security controls that work transparently without disrupting application functionality.
Q8. How can I start implementing mobile app security practices with Developer Bazaar Technologies?
You can contact our security specialists by clicking here or emailing us at [email protected] to start implementing comprehensive mobile app security practices today.

RM Mishra
Co-Founder
Developer Bazaar technologies